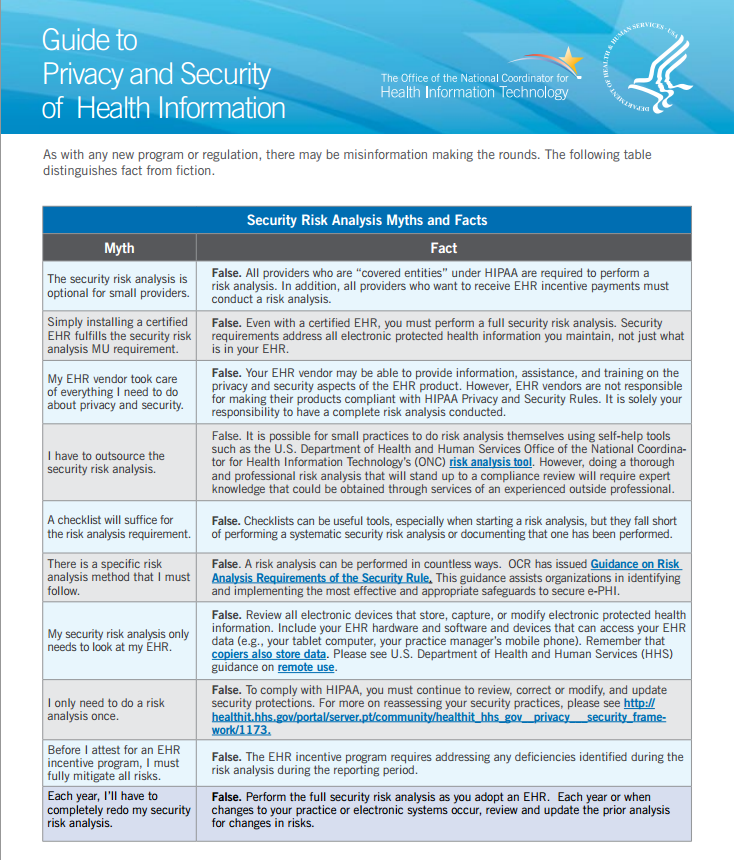
The office of National Coordinator for Health Information Technology (ONC) has published a useful guide to Privacy and Security of Health Information (PDF). One of the sections looks at common myths and facts about a security risk analysis / assessment. Let’s take a look at it in more detail. Below are ONC’s myths and facts:
Let’s look at a few of the myths:
- The first myth looks at small practices and if a security risk assessment is required. When the HIPAA security rule was introduced it required covered entities to be in compliance as of April 21, 2005. Small covered entities were given an extra year to comply until April 21, 2006 (yes that was over 6 years ago!). So although smaller practices were given more time for compliance they are still required to comply with the HIPAA security rule and perform a risk assessment.
-
- The second myth looks at Meaningful Use. In order to attest for meaningful use, a practice not only needs to implement a certified EHR but also needs to perform a risk assessment on how the organization is protecting electronic health information (ePHI). An important point to highlight is that the risk assessment needs to look at all ePHI not just ePHI stored in an EHR.
- The forth myths looks at whether a covered entity needs to outsource the risk assessment. It is not required to outsource the risk assessment and covered entities can do it themselves. NIST has a risk assessment tool that can be used and there are various self assessment tools on the market. But ONC makes an important disclaimer. If an organization wants to do a thorough risk assessment it requires experts. Self assessments are helpful in identifying some risks but experts have a thorough understanding of the HIPAA security rule, threats and vulnerabilities to ePHI and will be able to provide much more insight into an organization’s risks to ePHI.
However, doing a thorough and professional risk analysis that will stand up to a compliance review will require expert knowledge that could be obtained through services of an experienced outside professional.
-
- Myth 7 addresses whether the risk assessment for Meaningful Use should only address the certified EHR. We hear this myth all the time. A security risk assessment needs to look at all systems that store, modify or transmit ePHI. This includes portable devices such as laptops, smartphones, tablets, USB drives, DVDs, etc. ePHI could also be stored in spreadsheets and documents, medical equipment such as ultrasounds and digital x-rays.
-
- Myths 8 and 10 look at the frequency of performing risk assessments. A covered entity must perform a risk assessment and then continue to update the risk assessment. It should be looked at as an iterative process. Although the HIPAA security rule does not state the frequency of performing updates to the risk assessment ONC recommends that this should be done at least once a year or when changes to your practice or electronic systems occur. This means that a risk assessment performed 3 years ago that has not been updated will not satisfy the HIPAA requirement.
- Myth 9 looks at what a covered entity must do to attest for Meaningful Use. This is another myth that we are asked all the time. Does an organization need to fully mitigate all risks? An organization does not need to mitigate all risks but they do need to address each of them and put a plan together to mitigate the risks.
ONC did a good job here shedding light on common questions and misconceptions. What is clear is that to comply with HIPAA and Meaningful Use requires performing a risk assessment and periodically updating the risk assessment.


Leave a Reply