By now you may have heard about the 6 million passwords that were stolen from LinkedIn. The passwords were posted on a Russian online forum. The passwords were encrypted but through the use of password cracking programs many of the passwords have been cracked.
An article over at IT security company Qualys goes into details on how they went about cracking 2 million of the 6 million passwords. The article is pretty technical but it explains how using dictionaries of common words help crack the passwords.
This clearly shows that no matter how elaborate a password you choose, as long as it is based on words and rules, even if there are many words and many rules, it will probably be cracked. The fact is that on a huge file like the LinkedIn leak, every password you find can help you to get another one. That is because human-created passwords are not random, and programs like John the Ripper and dictionary attacks can use patterns, either already known or discovered in the password hash file, to greatly reduce the time needed to crack them.
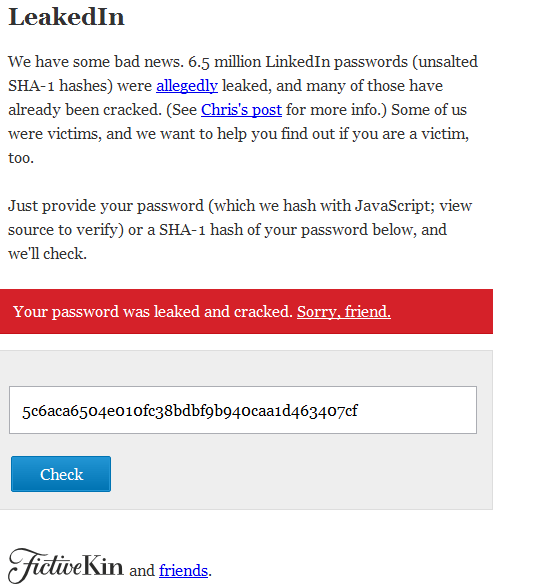
Not all of the 6 million passwords have been cracked. There are websites popping up that let you check to see if your LinkedIn password was one of the ones that were cracked. One site called LeakedIn let’s you put in your password and check to see if it was one of the cracked passwords.
There are some takeaways from the LinkedIn password hacking that everyone should consider.
- The use of passwords that are based on common words should not be used
- Do not use passwords based on common words even if you replace letters. They can still be cracked
- Do not use the same password at multiple sites. If your password is cracked at one site it can be used to gain access at multiple sites
- Always use complex passwords. The more sensitive the data on the site, the more complex the password should be
Our video below will help you understand and use complex passwords.
Click on ![]() above to view in fullscreen mode!
above to view in fullscreen mode!



Leave a Reply