Educating employees on security awareness and the dangers posed by cybercriminals is critical to any organization. While you can train employees on what to look for and how to best protect your practice, cybercriminals will continue to find unique and more sophisticated ways to trick individuals and gain access to the sensitive data they’re trying to protect. The key to truly protecting an organization may lie in acknowledging that there is no 100% fool-proof way to keep the criminals out.
Vanderbilt University Medical Center (VUMC) admits that while they are doing an outstanding job in educating their workforce and implementing technical safeguards to keep the bad guys out of their organization, they still get in. Health IT Security looks at how VUMC discovered their employees were being phished and what remediation steps were put in place to further improve their security measures to protect all applications and accounts.
Phishing remains a favored method of attack for cybercriminals due to the human factor. Organizations can put as many safeguards as possible in place to protect themselves in a technical sense, but all it takes is one employee to make a mistake to undo all of that.
VUMC, who has a plethora of safeguards in place to protect their organization has recently been targeted by cybercriminals attempting to phish their employees. Cybercriminals often carry out spear-phishing attacks, targeting specific individuals who the hacker may have information on, making them appear to come from a legitimate source.
Cybercriminals were targeting VUMC staff in an attempt to trick them into exposing their credentials to the HR site used to track direct deposit status, bank account info, and more. According to Andrew Hutchinson, Executive Director of Enterprise Security, hackers were able to change direct deposit information after obtaining credentials to have employees’ paychecks deposited to their own bank accounts. Luckily, VUMC quickly caught on after an employee reported not receiving their pay.
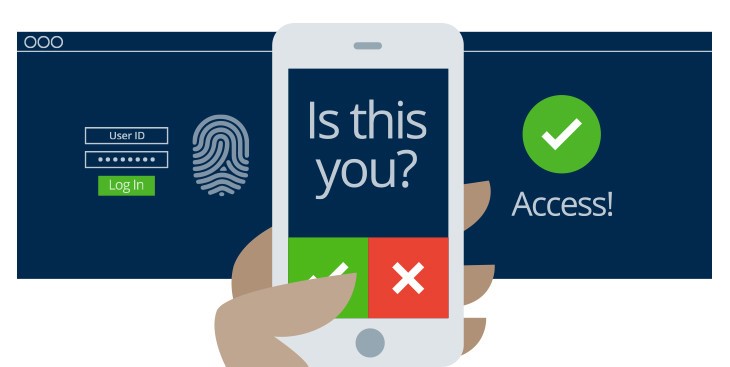
Although the hospital did have 2-factor authentication (2FA), or multi-factor authentication, across various applications at the time of the phishing attacks, some applications did not, including the HR portal. Now, VUMC has started adding 2FA to all platforms, which will require two forms of identification to gain access to the system. Early stages of the 2FA rollout were done on an optional basis, but as of Nov. 19th, the hospital will be requiring it for certain components where Personally Identifiable Information (PII) or other sensitive data may be kept.
The hospital has also ensured that all employees will have a way to utilize 2FA. They are offering the multi-factor authentication through a smartphone application, text message, or a key fob for employees who do not have a cell phone. The hospital is also allowing employees to go to express locations to pick up physical copies of their direct deposit forms, W2s, etc. if they would rather not use the HR portal at all.
Hutchison explains that the hospital does an excellent job of educating users on various security measures. Education is routinely provided regarding the use of multi-factor authentication, and phishing by sending out simulated phishing attacks, however, cybercriminals can still find ways into any system. To combat that, VUMC plans to continue forward with implementing any additional security measures they see fit and continuing to educate the workforce.


Leave a Reply