You get an email or text from what seems to be a legitimate email or phone number. Then you read the message: “Send bitcoin right away or else I am sending compromising photos or information to your friends and family.”
If you’ve received this type of email, you’ve likely been a victim to a new variation of an old scam. This type of fear-inciting message has you unsure of the nature of what they are talking about, the items that they may or may not have, or the possibility of any one of your various digital devices being hacked. Even if you know the claim is impossible and untrue, the message is still unsettling and honestly, a bit frightening. This new twist on old ways is identified as sextortion and it plays on the fear of the unknown.
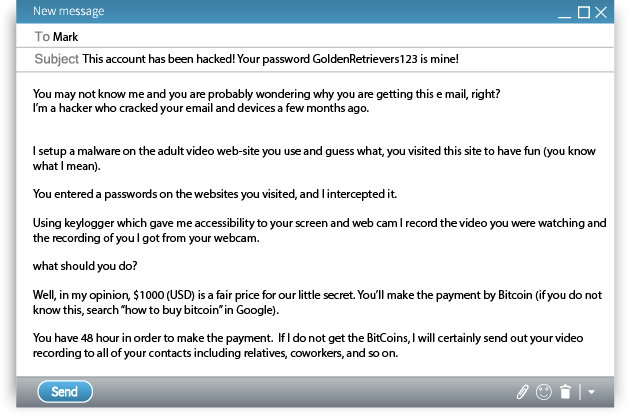
Here’s how the scam works:
The hacker indicates that they have gained access to your device and will release embarrassing information. You don’t know if it is photos, emails, or text messages, and your mind begins to race. Typically, the scammer threatens to disperse this information to your employer, friends, and family, with very vague threats as to what type of content they have. In some instances, the hacker may make very detailed claims about the contents they are allegedly in possession of.
So, what do they want? To avoid having the damaging content exposed, the cybercriminal will request an immediate transfer of funds, sometimes thousands of dollars, typically through bitcoin.
What would make an individual believe these claims are true even when they know it can’t be or is highly unlikely? It all comes down to the scammer’s credibility, which is established when they provide you with a password from one of your accounts. They may not always identify which account they have obtained it from, but it is likely that this information was purchased on the dark web. By matching up emails and passwords of often millions of people, they can count on at least a small percentage of their chosen victims to react and pay.
Before your fear levels elevate and you start searching for how to purchase Bitcoin, or what exact information they could have, take a deep breath and rest assured, you’re very likely being played. Don’t fall for it, and don’t pay the ransom.
If you are provided with a legitimate password, stop using it and change it immediately. Using a password manager will assist you in keeping track of your passwords by creating one strong password that is difficult to hack. Never reuse the same password. If you have done so in the past, it is highly recommended that you update them. A combination of letters, numbers, punctuation and capital letters increases your password security. You may want to consider using a hard to guess passphrase when you’re creating passwords.
Be sure to enable two-factor authentication when you’re able.
Cover the camera lens on your computer by using electrical tape or purchasing a camera cover.
And finally, don’t respond to these email requests. The more that you respond, the more likely you are to expose more information for them to manipulate against you.



Leave a Reply