 When it comes to HIPAA compliance, it’s easy to feel as if you’re being pulled in a million different directions at once. In part, this could be due to the fact that there are 4 different rules that go into HIPAA: the Privacy Rule, the Security Rule, the Breach Notification Rule, and the Omnibus Rule.
When it comes to HIPAA compliance, it’s easy to feel as if you’re being pulled in a million different directions at once. In part, this could be due to the fact that there are 4 different rules that go into HIPAA: the Privacy Rule, the Security Rule, the Breach Notification Rule, and the Omnibus Rule.
Let’s take a look at the first two, which are in most cases, the most important to understand for day-to-day compliance. By exploring the differences between HIPAA’s Privacy and Security rules, you can identify current risks your practice may be facing and create comprehensive policies and procedures to mitigate them.
The HIPAA Privacy Rule: Think “Patient Privacy”
The HIPAA Privacy Rule regulates the use and disclosure of protected health information (PHI) by covered entities. Covered entities include healthcare providers, health plans, and healthcare clearinghouses. This rule gives patients the right to access their own medical records and restricts the use and disclosure of PHI to anyone other than their authorized representatives.
The Privacy Rule also requires covered entities to implement administrative, physical, and technical safeguards to protect PHI from unauthorized access, use, or disclosure. You can read our strategies for what this should look like in the office (link to safeguards) and the waiting room (link to the waiting room). By designating a privacy officer, covered entities ensure that developing and implementing privacy policies and procedures remains a top priority.
The HIPAA Security Rule: Think “Everything IT”
The HIPAA Security rule, on the other hand, deals with the protection of electronic PHI (ePHI). The Security rule also requires the implementation of safeguards, but this time to protect ePHI from unauthorized access, use, or disclosure. It applies to all forms of ePHI, including data stored on computers, servers, and mobile devices. Regular risk assessments are required to identify potential system vulnerabilities and appropriate steps to mitigate those risks.
While oftentimes these responsibilities can be passed off to IT, it is crucial that all staff members remain up-to-date on cybersecurity procedures to protect against human error, the primary cause of cyberattacks.
Key Differences
The Privacy Rule deals with all forms of PHI, whereas the Security Rule specifically applies to ePHI. Additionally, the Privacy Rule focuses on the use and disclosure of PHI, while the Security Rule focuses on the protection of ePHI.
We also designed this infographic for our visual learners.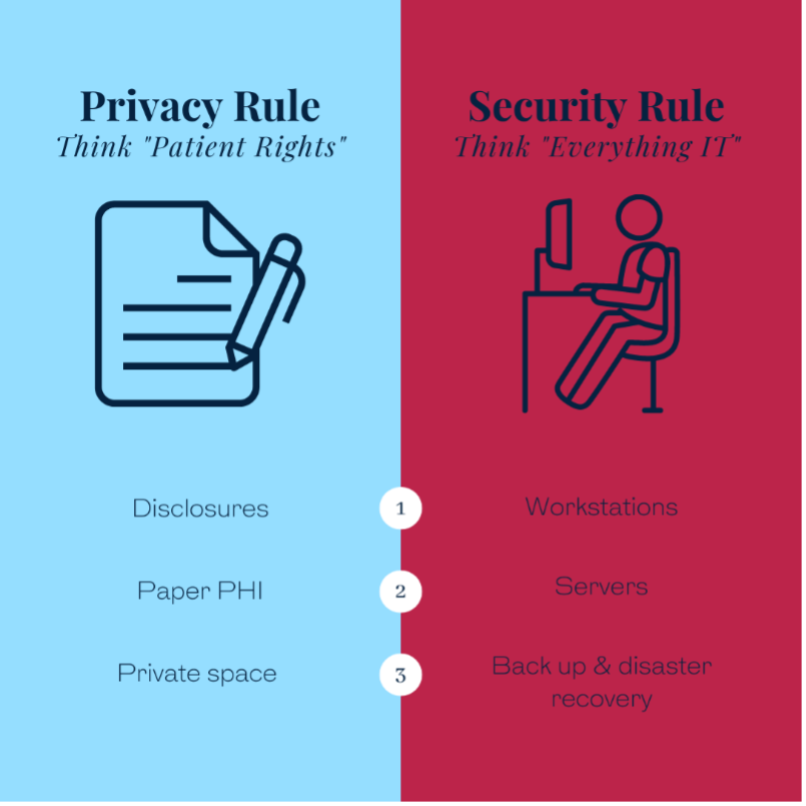
While these differences may seem subtle, they are important for healthcare providers to understand. Compliance with both the Privacy Rule and Security Rule is critical to protecting patient privacy and maintaining the integrity of ePHI. Failure to comply with these rules can result in significant fines and legal action.
The HIPAA Privacy and Security rules serve distinct purposes in regulating the use and protection of PHI and ePHI, respectively. As a healthcare administrator, it is essential to have a thorough understanding of both rules and to implement appropriate policies and procedures to comply with them. This includes designating a privacy officer, conducting regular risk assessments, and implementing technical and physical safeguards to protect ePHI. By following these guidelines, healthcare organizations can protect patient privacy and maintain the integrity of ePHI while complying with HIPAA regulations.

Leave a Reply