- All
- Backup & Disaster Recovery
- Business Associates
- Client News
- Healthcare Industry
- HIPAA
- HIPAA Audits
- HIPAA Violations
- HSN News
- Legal
- MACRA
- Policies and Procedures
- Press Release
- Remote Workforce
- Risk Assessment
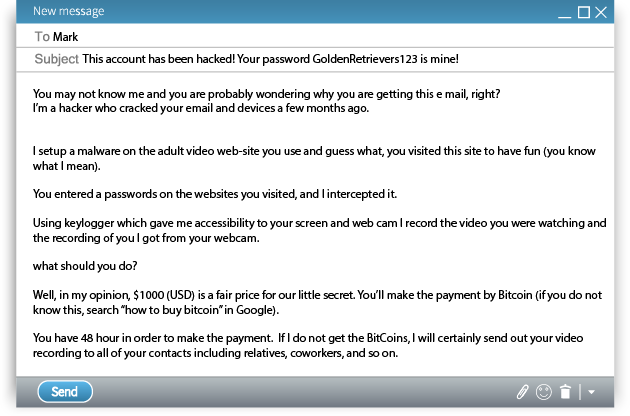
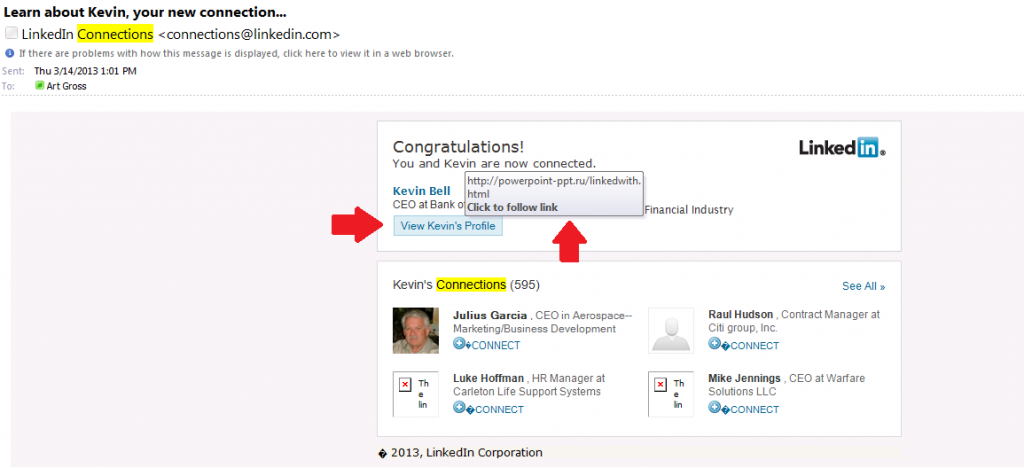
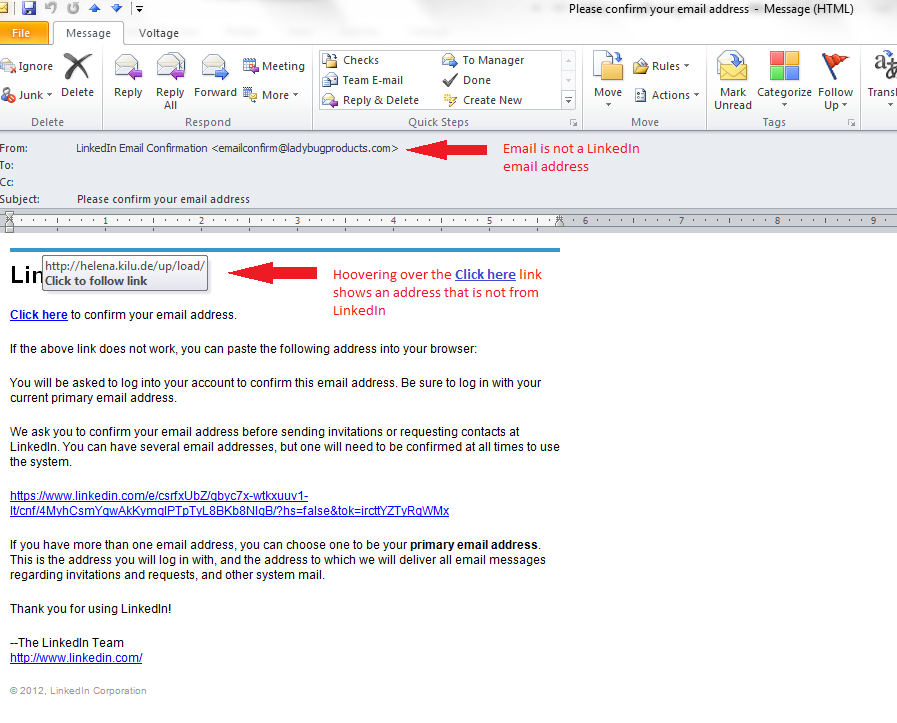
- Scams
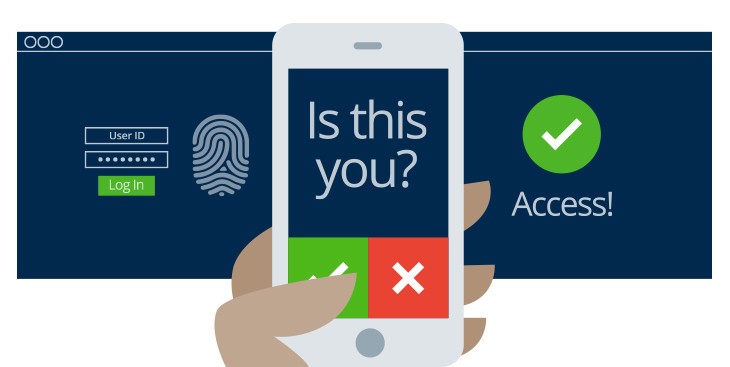
- Security
- Security Reminders
- Security Training
- Telehealth
- Website
HIPAA Secure Now Pairs Productivity with Cybersecurity Training to Boost Outcomes
April 1, 2024
Navigating the Threat Landscape: Common Cybersecurity Risks and Solutions for Healthcare Providers
February 2, 2024
Social Engineering in Healthcare: Recognizing and Mitigating the Human Factor
November 17, 2023
Caught off Guard: What the Pandemic Taught Healthcare Organizations About Being Prepared for a Business Interruption
August 4, 2020
HIPAA Secure Now Joins Far-Reaching Initiative to Promote the Awareness of Online Safety and Privacy for National Cybersecurity Awareness Month
October 1, 2019
HIPAA Secure Now Joins Far-Reaching Initiative to Promote the Awareness of Online Safety and Privacy for National Cybersecurity Awareness Month
October 1, 2019
Right to Access was Implemented to Protect Patients but is Hurting Patients & Providers Alike (Part 2)
September 23, 2019
Right to Access was Implemented to Protect Patients but is Hurting Patients & Providers Alike (Part 1)
September 17, 2019
Lawsuit Filed Against the University of Chicago Medical Center and Google over Data Sharing
July 1, 2019
7,038 Patients of Pawnee County Memorial Hospital Notified of Phishing Attack
March 18, 2019
HHS Cybersecurity Guidelines: The 6 Simple Steps That Will Mitigate The Top 5 Threats To Healthcare
February 1, 2019
Ransomware Is Alive and Well – Here Are 10 Tips to Help Protect Your Organization
January 22, 2019
HIPAA Violations During ‘Boston Med’ Filming Leave Three Boston Hospitals with $999,000 in Fines
September 24, 2018
Healthcare Data Breaches Rise Along with Consumer Concerns of Privacy and Data Security
August 20, 2018
Healthcare Data Security: Less of a Concern for U.S. Adults than Threats to Financial Information
August 6, 2018
HHS’ OCR proposes HIPAA change to share settlements of data breaches with victims
May 29, 2018
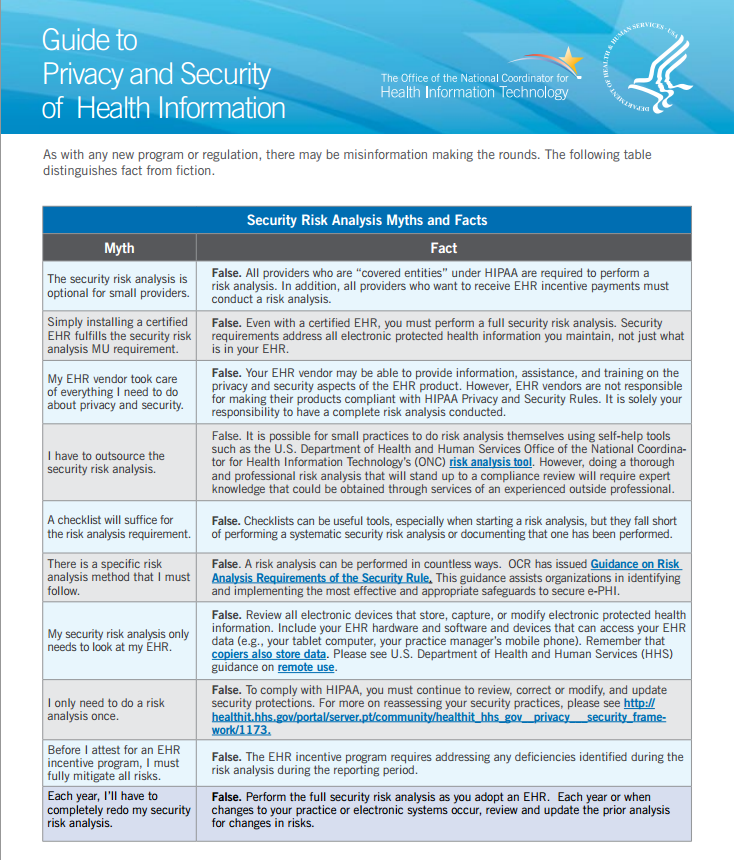
OCR Cyber Security Newsletter: Risk Analyses vs. Gap Analyses – What is the difference?
April 30, 2018
HIPAA Secure Now! Chosen as Preferred Vendor for 2,700 YMCAs Across the United States
December 4, 2017
HIPAA Secure Now! Joins Forces with MyMipsScore to Aid Physicians in Raising MIPS Scores and Medicare Reimbursements
December 1, 2017
56% of healthcare organizations see employees as their greatest threat to IT security
August 4, 2017
Article: 68 percent of healthcare organizations have compromised email credentials
May 1, 2017
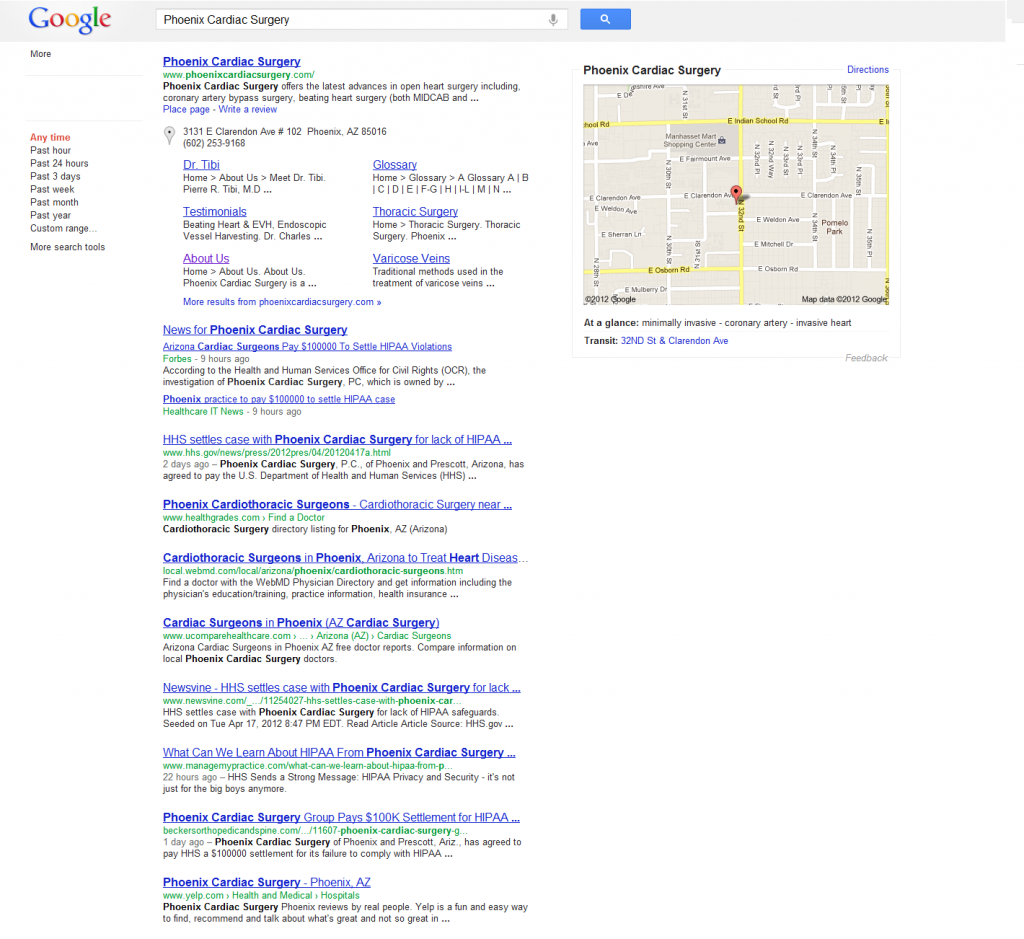
Office for Civil Rights Issues Second Largest HIPAA Fine to Date – $5.5 Million
March 22, 2017
Article: Snooping St. Charles Health System Employee Accessed Almost 2,500 Patient Records
March 20, 2017
New CMS MACRA Rule Kicks In, Factors HIPAA Compliance into New Payment Structure
November 30, 2016
New CMS MACRA Rule Kicks In, Factors HIPAA Compliance into New Payment Structure
November 30, 2016
MedSafe and HIPAA Secure Now! Announce Partnership to Offer Enhanced Healthcare Compliance Solutions
May 27, 2016
Computer Fraud and Abuse Act may help companies against employee cyber theft
November 5, 2015
Excellus Blue Cross Blue Shield Breach Yet Another Sign To Step Up Health-Care Security Investment
September 15, 2015
HIPAA Secure Now! Appoints Jonathan Krasner to Head Business Development, Grow MSP Partner Base, Help Partners Succeed
June 4, 2015
HIPAA Secure Now! Appoints Jonathan Krasner to Head Business Development, Grow MSP Partner Base, Help Partners Succeed
June 4, 2015
MSP Differentiates His Business With HIPAA, SMB Security, Expands Partner Program
February 12, 2015
The ASCII Group Names HIPAA Secure Now! Esteemed Noble Partner at ASCII Success Summit 2014
November 18, 2014
The ASCII Group Names HIPAA Secure Now! Esteemed Noble Partner at ASCII Success Summit 2014
November 17, 2014
HIPAA Secure Now! Signs Agreement with the American Osteopathic Association (AOA), Provides Full Array of HIPAA Compliance Services to 100,000-Plus Members
October 21, 2014
HIPAA Secure Now! Signs Agreement with the American Osteopathic Association, Provides Full Array of HIPAA Compliance Services to 100,000-Plus Members
October 14, 2014
HIPAA Secure Now! Ramps up EHR Partner Program, Helps Healthcare Providers Achieve Meaningful Use under Revised CMS Deadlines
August 21, 2014
HIPAA Secure Now! Ramps up EHR Partner Program, Helps Healthcare Providers Achieve Meaningful Use under Revised CMS Deadlines
August 21, 2014
HIPAA and the Cloud: How to Securely Store and Share Patient Files with Dropbox
August 14, 2014
Good infographic on the need to implement secure communications to protect patient information
July 23, 2014
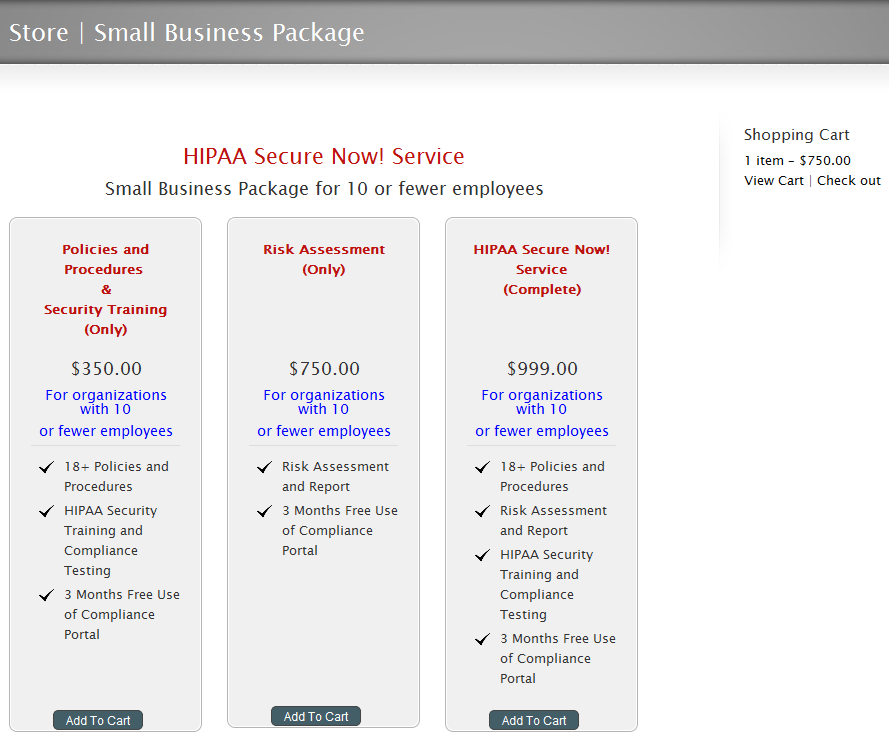
HIPAA Secure Now! Offers Annual HIPAA Security Training Subscriptions for Employees of Covered Entities and Business Associates
June 23, 2014
HIPAA Secure Now Voted Best Vendor at ASCII IT SMB Success Summit in Austin, TX
March 26, 2014
HIPAA Secure Now! Announces a Low Cost $399 HIPAA Security Service Aimed at Small Organizations
December 10, 2013
The AMA releases toolkit to help organizations comply with HIPAA Omnibus Rule
September 9, 2013
HIPAA Secure Now! includes $100,000 financial protection from HIPAA breach and violation expenses
July 23, 2013
HIPAA Secure Now! and BUMI Partner to Provide a HIPAA Compliant Data Backup Service
May 21, 2013
Healthcare Providers Insurance Exchange (HPIX) and HIPAA Secure Now! Announce Partnership
July 27, 2012
Recent Posts
- Third-Party Risk Management in Healthcare
- Beyond Compliance: Elevating Cybersecurity for Long-Term Success
- HIPAA Best Practices and Priorities for 2024
- HIPAA Secure Now Pairs Productivity with Cybersecurity Training to Boost Outcomes
- Platform-Specific Cybersecurity Training in Microsoft 365 and Google
Archives
- April 2024
- March 2024
- February 2024
- January 2024
- December 2023
- November 2023
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- May 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- January 2014
- December 2013
- November 2013
- October 2013
- September 2013
- August 2013
- July 2013
- June 2013
- May 2013
- April 2013
- March 2013
- February 2013
- January 2013
- December 2012
- November 2012
- October 2012
- September 2012
- July 2012
- June 2012
- May 2012
- April 2012
- March 2012
- February 2012
- January 2012
- December 2011
- November 2011
- October 2011
- September 2011
- August 2011
- July 2011
- June 2011
- May 2011
- April 2011
- March 2011
- February 2011
Categories
- Backup & Disaster Recovery
- Business Associates
- Client News
- Download
- Healthcare Industry
- HIPAA
- HIPAA Audits
- HIPAA Violations
- HSN News
- Legal
- MACRA
- Policies and Procedures
- Press Release
- Remote Workforce
- Risk Assessment
- Scams
- Security
- Security Reminders
- Security Training
- Telehealth
- Uncategorized
- Webinar
- Website























































































































































































































Recent Comments